By: Xiaolong Guo, Xuan Zhang, and Yier Jin
Stage: RTL
Summary
- The absence of standard board-level attack benchmark prevents credible and verifiable comparisons among different techniques.
- PCBench is a comprehensive set of open-source board-level attack benchmarks and a benchmark generation mechanism.
- A systematic definition and a comprehensive taxonomy of board-level attacks.
- A wide range of board-level attacks are designed and integrated. PCBench can be used to provide references for countermeasures evaluation
- PCBench can be used to provide references for countermeasures evaluation.
Motivation
- Most modern electronic systems are hosted by printed circuit boards(PCBs), making them a ubiquitous system component that can take many different shapes and forms. In order to achieve a high level of economy of scale, the global supply chain of electronic systems has evolved into disparate segments for the design, fabrication, assembly, and testing of PCB boards and their various associated components.
- As a consequence, the modern PCB supply chain exposes many vulnerabilities along its different stages, allowing adversaries to introduce malicious alterations to facilitate board-level attacks. As an emerging hardware threat, the attack and defense techniques at the board level have not yet been systemically explored and thus require a thorough and comprehensive investigation.
- In the absence of a standard board-level attack benchmark, current re-search on perspective countermeasures is likely to be evaluated on proprietary variants of ad-hoc attacks, preventing credible and verifiable comparison among different techniques. Upon this request, we have created the PCBench, which is a set of board-level attack benchmarks for open-source release.
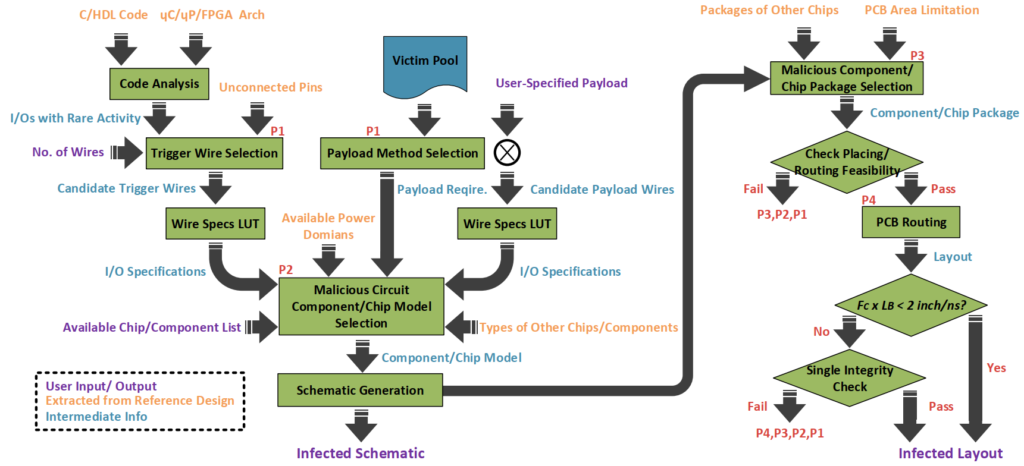
Benchmarking Methodology
- A broad range of board-level attacks are defined and categorized.
- For the first time, the attack vectors and construction rules for board-level attacks were developed.
- A practical and reliable board-level attack benchmark generation scheme was also developed, which can be used to produce references for evaluating countermeasures.
Released Benchmarks
- To facilitate the development of board-level attack benchmarks, representative circuit boards are chosen as the victim designs. Open-source hardware projects are mainly selected due to their modern design styles, the availability of PCB designs as well as detailed documents, firmware, and/or application software. As a result, researchers can easily reconstruct the board-level security evaluation benchmarks.
- The following table lists the released benchmarks:
| Design Name | Description | Dimension (mm^2) | No. of Components | No. of Layers |
| arduino-due | Microcontroller devlopment board based on ATsam3x8e with ARM Cortex-M3 core | 102×53 | 141 | 2 |
| a13-olinuxino | Single-board Linux computer based on Allwinner-A13 with Cortex-A8 core | 120×120 | 370 | 4 |
- Note that This is not the full list of benchmarks as we continue developing the new benchmarks.
- The fabricated Arduino-due board with and without Trojans are shown below.

Contact
Input/Output Interface
- Input: PCB reference design and Board level attack vector
- Output: Board level Trojan inserted benchmark
Toolset can be found at: https://github.com/xz-group/PCBench
Licensing Info
https://github.com/xz-group/PCBench/blob/main/LICENSE
Dependencies
- Eagle: https://www.autodesk.com/products/eagle/overview?plc=F360&term=1-YEAR&support=ADVANCED&quantity=1
- KiCad: https://kicad-pcb.org/
References
PCBench: Benchmarking of Board-Level Hardware Attacks and Trojans Proceedings Article Forthcoming
In: IEEE/ACM Asia and South Pacific Design Automation Conference, Forthcoming.
Acknowledgments
- This work was partially supported by DARPA